Gödel's Ceiling
In 1931, Kurt Gödel published his two incompleteness theorems. The first theorem states that any consistent formal system powerful enough to express elementary arithmetic contains statements which are true but cannot be proven within the system. The second theorem states that such a system cannot prove its own consistency. Together, the theorems draw an absolute ceiling on what any mathematical system can establish about itself.
Cryptography is a subset of mathematics. Every deterministic cryptographic scheme — every block cipher, every PRNG, every public-key primitive — is a formal system in the Gödelian sense. The theorems apply. There will always be true statements about the scheme's behavior that the scheme cannot prove. In practice, those statements are the ones adversaries exploit.
Why Math Fails at Scale
If we scale cryptographic session keys to the infinite numbers that heavy Zero Trust architectures demand — tens of thousands of keys per second, rotated constantly, across millions of endpoints — the complexity crosses a Turing threshold. Eventually, deterministic algorithms loop predictably or enter mathematically unsolvable states. The ceiling Gödel drew becomes a floor the system collides with.
The Three Collision Points
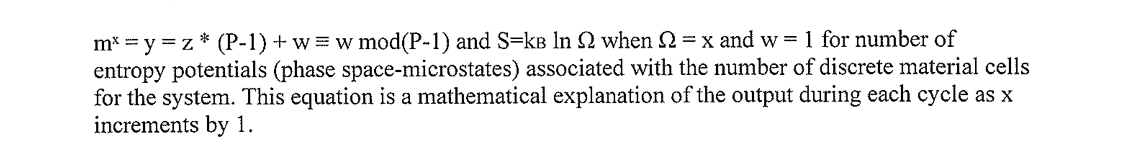
In Dr. White's framing, three collision points appear whenever a deterministic scheme is pushed to operational scale:
- Periodicity. Every PRNG has a period. At sufficient draw rates, the period is reached and the output repeats. This is not a flaw in a particular algorithm; it is a property of all algorithms.
- Undecidability. For any chosen bit of the output, there exist input conditions under which the system cannot decide the bit's value consistently. Gödel's first theorem guarantees these conditions exist.
- Self-referential failure. Any attempt to prove the scheme secure using the scheme itself (e.g. signing a consistency claim with a key derived from the same cipher) runs directly into Gödel's second theorem.
Rejecting Determinism to Bypass Gödel
ATOFIA deliberately rejects deterministic math to bypass Gödel's constraints entirely. Our entropy does not rely on a series of formulas; it is measured physically. A physical measurement is not a formal system. It cannot be subjected to incompleteness critique because it does not make axiomatic claims — it reports the state of a thermodynamic process.
This is the single most important structural property of thermodynamic cryptography, and it is routinely missed by analysts who try to evaluate ATOFIA the way they would evaluate a new PQC candidate. ATOFIA is not a new algorithm competing on mathematical hardness. It is a category shift away from algorithmic trust to physical trust.
Incorporating Looping for Absolute Variance
To protect the output sequence from any residual structure, ATOFIA incorporates continuous topological loops in the mixing protocol. These loops ensure that even the spatial arrangement of successive microstates varies in a way that cannot be reduced to a generator function. Topology provides what algebra cannot: a notion of continuous deformation that preserves randomness across reconfiguration.
"The invention and percolation of algorithms sparked rapid growth… but entropy procedures should provide randomness independent of a mathematical function. A computational algorithm lacks the incompleteness and undefined needed for staging reconstituted probability descriptions." — Dr. Thurman Richard White, ATOFIA
Implications for Post-Quantum Standards
Most post-quantum proposals retain the algorithmic premise. They substitute one hard problem (factoring, discrete log) for another (lattice, code, isogeny) and trust that the substitution will outlast the next generation of adversaries. Gödel's theorem applies to the replacements exactly as it applies to the originals. A lattice-based scheme is a formal system; there will be true statements about it that the system cannot prove. Somewhere in that gap, future adversaries will operate.
Thermodynamic cryptography does not close the gap — it moves the anchor out of the formal system entirely. The resulting security does not rest on the assumption that a particular math problem is hard. It rests on the assumption that physics is physics. This is the strongest assumption available to any security architecture.
Why This Matters for Zero Trust
Zero Trust architectures generate, distribute, and rotate vastly more key material than the cryptographic systems of a decade ago. Every machine-to-machine authentication, every microservice handshake, every short-lived workload identity demands fresh entropy. In a Zero Trust deployment built on deterministic sources, Gödel's ceiling is reached daily rather than annually. The only sustainable anchor for Zero Trust at scale is one that does not participate in the formal system at all.
A Category Shift, Not a New Algorithm
One reason the incompleteness implication has been ignored by mainstream cryptography for so long is that every proposed response within cryptography has been another algorithm. The field has essentially spent ninety years looking for a mathematical scheme to escape a mathematical problem. Gödel himself would have predicted the outcome: each new scheme inherits the same ceiling. Only a category shift — from algorithmic generation to physical measurement — escapes the theorem's domain. Thermodynamic cryptography is that category shift.
This framing also clarifies why ATOFIA's work is misunderstood when evaluated with conventional cryptographic benchmarks. Benchmarks measure rate, key size, and bit-level resistance to known attacks; they assume the primitive is a function whose security reduces to the hardness of a mathematical problem. A thermodynamic primitive has none of these properties. It does not have a "key size" in the conventional sense because it does not generate keys algorithmically; it measures a physical process and returns the reading. Benchmarking it against AES is like benchmarking a ruler against a stopwatch — both are measurement tools, but they measure categorically different quantities.
What Remains Trusted
Moving the anchor out of the formal system does not eliminate the need for cryptographic primitives above it. Encryption still needs a cipher; authentication still needs a MAC; integrity still needs a hash. What changes is the source these primitives consume. Today, they consume PRNG output seeded from a weakly-entropic source; tomorrow, under a thermodynamic anchor, they consume physical microstates directly. The algorithms remain, but their inputs are no longer subject to Gödel's constraint, which means the overall system's security claim is no longer subject to it either. The algorithms have become thin layers of formatting above a substrate they cannot compromise.