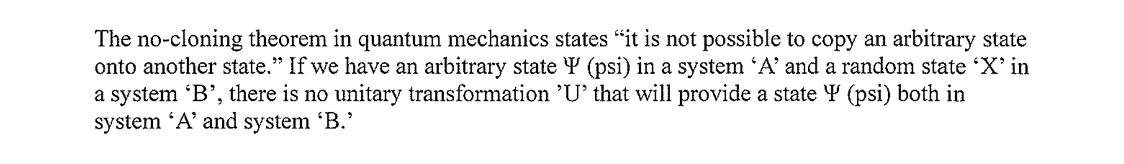
What the No-Cloning Theorem Actually Says
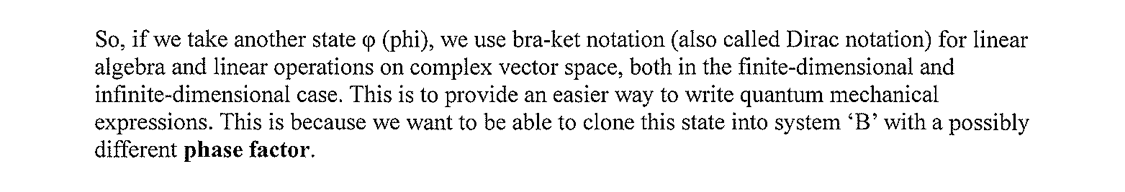
The No-Cloning theorem heavily influences quantum mechanics. Its statement is short: it is not possible to copy an arbitrary state onto another state. Formally, given an arbitrary state Ψ in system A, there is no unitary transformation that produces Ψ in system B without destroying the original.
Why Pseudorandom Session Keys Are Cloneable
When session keys are generated pseudo-randomly, the value produced is not an arbitrary state. It is the deterministic output of an algorithm seeded by harvested entropy. The algorithm is fully knowable; the seed is approximately knowable; the output is therefore reproducible by any adversary who can model the inputs. Cloning the session key is not a physics violation — it is a software exercise.
Forcing a Quantum-Statistical Authentication Vector
By using physical topological entropy generated by ATOFIA mixing protocols, we move the authentication vector out of the algebra of computation and into the statistics of physical sampling. The session key is no longer the output of a function; it is a measured microstate that existed for the duration of the sampling event and is gone afterward.
What This Buys You
- Replay attacks fail. The next session key has no algorithmic predecessor for an attacker to recompute.
- Side-channel leakage degrades cleanly. Information leaked about one session does not generalize to the next.
- Quantum advantage does not help. The adversary's ability to factor or search is irrelevant when there is nothing to factor or search.
The Practical Cryptographic Consequence
By outsourcing randomness to thermodynamic unpredictability, you explicitly invoke the No-Cloning rule on your infrastructure. Replay attacks against your authentication channel become not just computationally hard but physically forbidden. The same property that makes quantum communication secure on a fiber link can be made to apply to a session key generated inside a server rack.