The Quantum-Safe Algorithm Is Not the Whole Stack
The NIST PQC standardization effort produced a generation of lattice-, code-, and hash-based algorithms designed to resist a cryptographically relevant quantum computer. The math is sound. The deployments are not. Every PQC implementation in the field today consumes randomness from the same place the algorithms it replaced did: a software pseudorandom number generator inside a virtualized operating system, seeded from kernel entropy that is itself manufactured from low-rate hardware events and software mixing.
If your post-quantum keys are seeded from a PRNG oscillating on top of a hypervisor, your quantum-safe keys are inherently compromised before they are ever stored.
The Problem of Decay
Mathematical strings lose their variance over time. When a closed sequence is processed without chaotic, uncompensated transformations, values inside the string begin to vanish — a representation of information damage we describe as algorithmic decay.
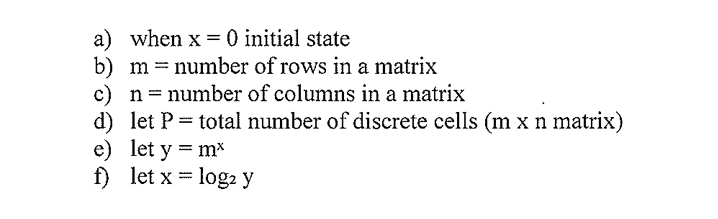
For PQC this matters in two specific places: long-lived signing keys (Dilithium, Falcon) where decay-induced bias accumulates statistically across millions of signatures, and ephemeral key encapsulation (Kyber) where a biased seed lets an offline adversary narrow the search space dramatically once a quantum computer is available.
Anchoring PQC to Physical Reality
To survive beyond the quantum cliff, PQC keys must be underpinned by Thermodynamic Reality — a continuous source of physical variance that is not being computed by the same machine that consumes its output. ATOFIA's Continuous Mixing Protocols (P+1, P−1) provide a sampled microstate at the moment a key is needed. The PQC algorithm receives an input it could not have predicted, and an adversary cannot reverse, regardless of quantum advantage.
Why a Physical Anchor Outlasts an Algorithmic One
- No long-lived seed. Each PQC keygen pulls a freshly sampled microstate; there is no master entropy pool to harvest.
- No statistical drift. Continuous thermodynamic mixing has no closed sequence to decay against.
- Algorithm-independent. Kyber, Dilithium, Falcon, SPHINCS+, and any future PQC primitive consume the same anchor without modification.
What This Means for "Harvest Now, Decrypt Later"
The practical adversary model behind PQC migration is HNDL: collect ciphertext today, decrypt it once a quantum computer arrives. The only defense is forward secrecy that survives a future computational breakthrough. Forward secrecy built on a software seed inherits the seed's weakness for the entire lifetime of the captured ciphertext. Forward secrecy built on a thermodynamic anchor inherits a property the adversary cannot circumvent: the next ephemeral key did not exist as a number anywhere in the system before it was sampled.